From Scanner to Stealer: Inside the trivy-action Supply Chain Compromise
An initial spike on Linux platforms linked to runners was observed on March 19, 2026. The…
An initial spike on Linux platforms linked to runners was observed on March 19, 2026. The…
Security analysts were spending the majority of their time on what leadership described as mechanical analysis….
Critical Vulnerability in Microsoft Devices Pricing Program CVE-2026-23651 and CVE-2026-26124 are Critical elevation of privilege vulnerabilities…
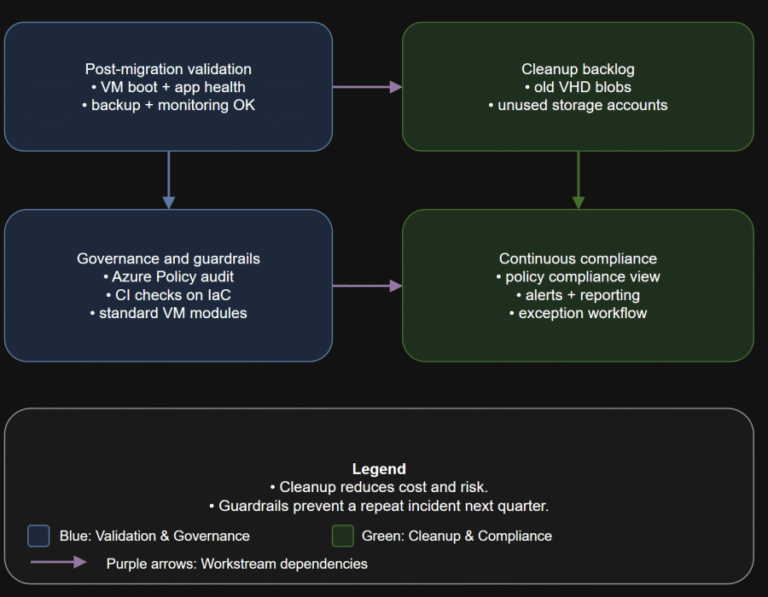
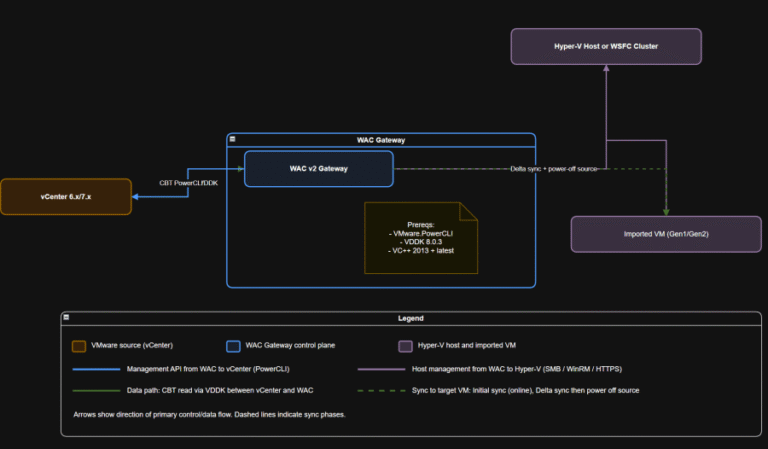
TL;DR Converting disks is not the finish line. Your real goal is a new steady state:…
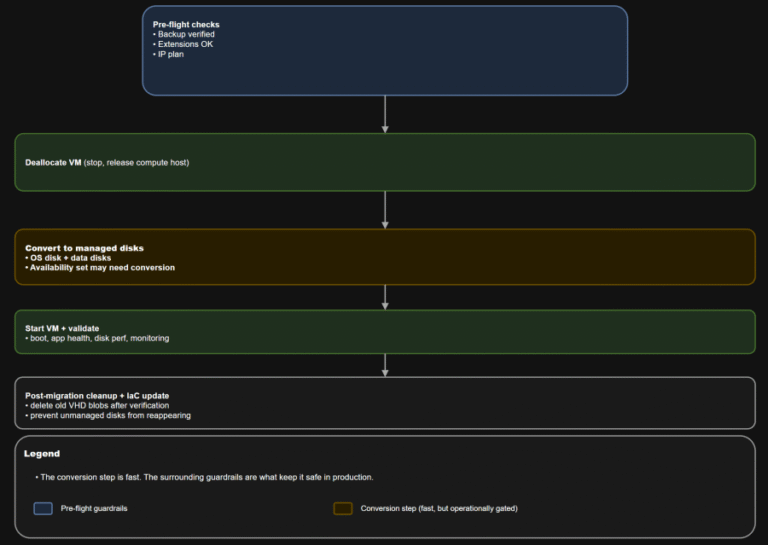
TL;DR Converting a VM to managed disks is usually operationally straightforward: deallocate, convert, start, validate. The…
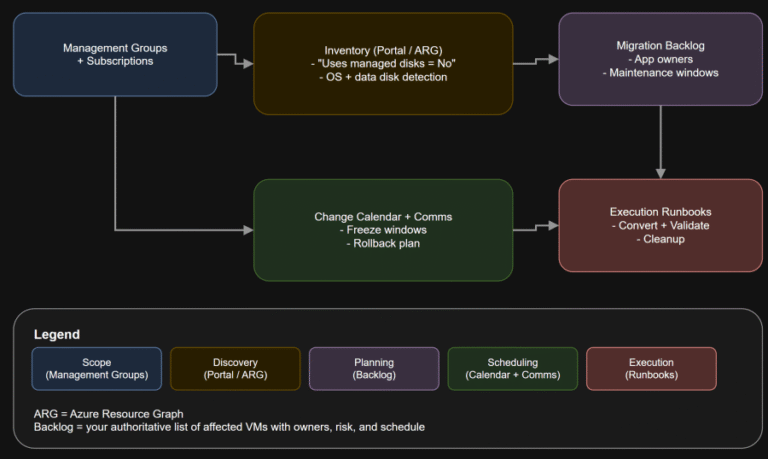
TL;DR If any Azure IaaS VM in your estate still uses unmanaged disks, it is on…
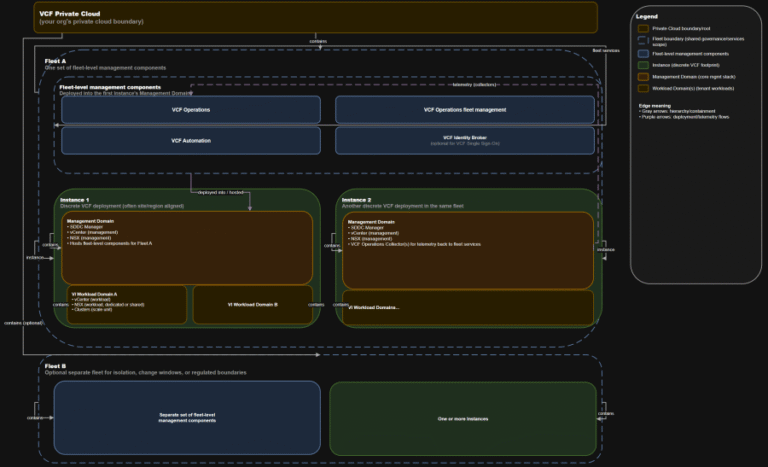
TL;DR A) One fleet, one instance, stretched where justified In VCF 9.0, identity is not a…
Actively Exploited Zero-Day Vulnerability in Windows Remote Desktop The vulnerability allows local attackers with no privileges…
As AI adoption accelerated, WEX® — a global commerce platform that supports business operations primarily for…
Unified classification: Apply consistent classifications for financial data, personally identifiable information (PII), protection health information (PHI),…

These reports include:With Falcon Cloud Security data correlated in Falcon Next-Gen SIEM, teams can detect cross-domain…
Windows 10 End of Support Is Here There is evidence of active exploitation in the wild…
For off-the-shelf capabilities like Bedrock or Vertex AI, Falcon Cloud Security identifies the APIs and services…
Compliance checkpoints (examples) Why this matters Bridge strategy: If you are standardizing on Windows Server and…
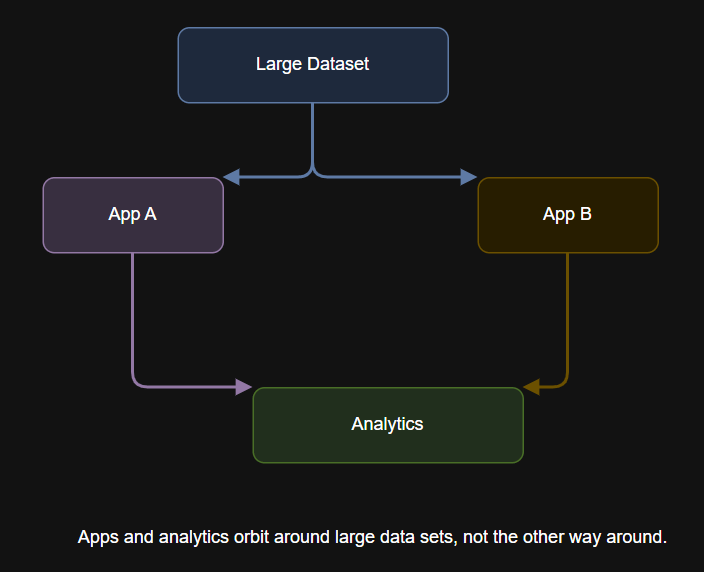
Table of Contents What Is Data Gravity? The History and Evolution of Data Gravity Why Data…