CrowdStrike Tailors Adversary Intelligence to Customer Environments
This enhanced workflow turns every indicator into actionable intelligence so teams can conduct smarter, faster investigations….

This enhanced workflow turns every indicator into actionable intelligence so teams can conduct smarter, faster investigations….
But with this integration comes risk. AI agents are often quickly deployed across SaaS environments by…
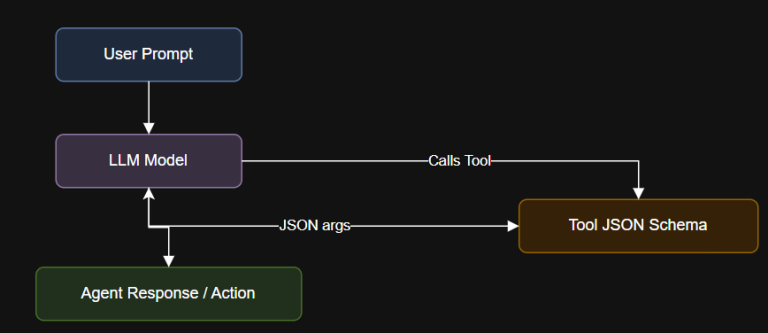
Introduction Function calling is the bridge between static LLMs and real-time agents. With tools like LangChain…
Today’s enterprising adversaries are weaponizing AI to scale operations, accelerate attacks, and target the autonomous AI…
But while AI empowers analysts to operate with greater speed and precision, this evolution is forging…
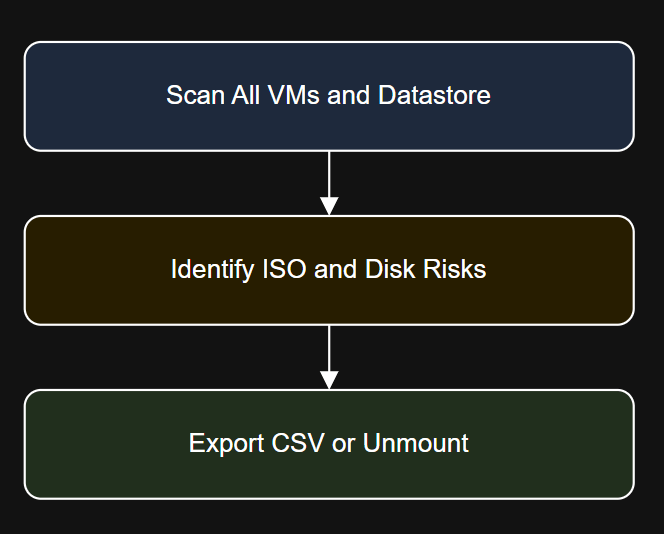
Introduction Get-VM | Where-Object {($_ | Get-HardDisk).Count -gt 3} | Select Name, PowerState, @{N=”DiskCount”;E={($_ | Get-HardDisk).Count}}…
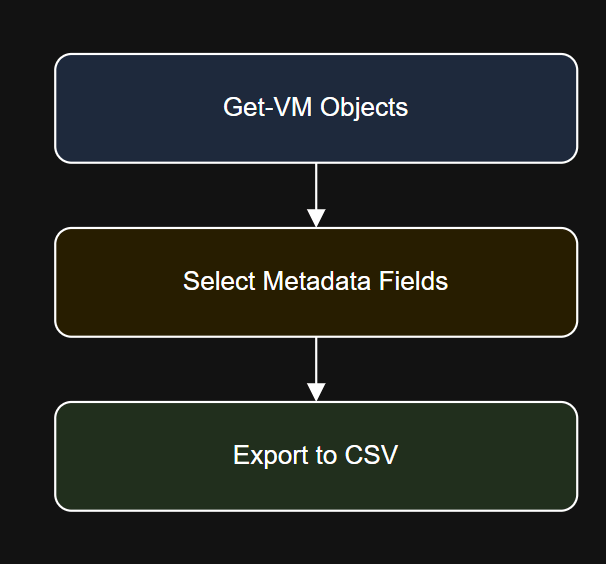
Introduction $timestamp = Get-Date -Format “yyyyMMdd”Export-Csv -Path “C:ReportsVM_Inventory_$timestamp.csv” -NoTypeInformation Step 4: Filter by Folder or Cluster…
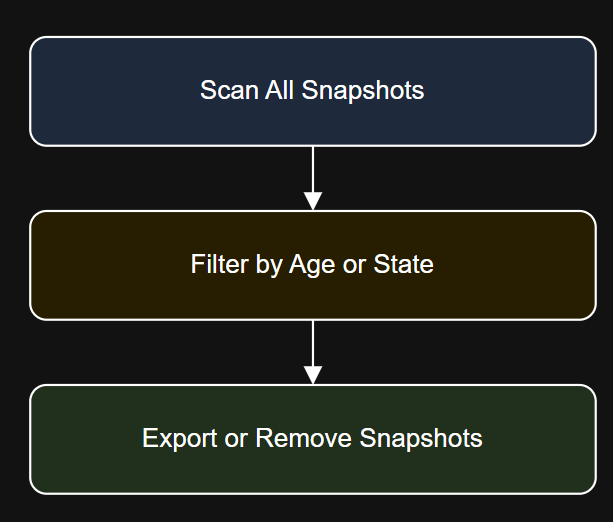
Introduction Get-VM | Where-Object {$_.PowerState -eq “PoweredOff”} | Get-Snapshot | Remove-Snapshot -Confirm:$false Diagram: Snapshot Lifecycle Workflow…
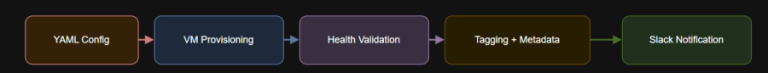
Introduction – name: Enterprise Nutanix VM Provisioninghosts: localhostgather_facts: falsecollections:- nutanix.ncpvars_files:- nutanix_credentials.yml- enterprise_vm_config.ymlvars:slack_webhook: “https://hooks.slack.com/services/XXXX/YYYY/ZZZZ”tasks:TASK [Check VM health]ok:…
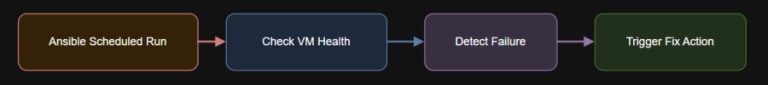
Introduction Nutanix Repository on GitHub My Personal Repository on GitHub Self-healing infrastructure reduces downtime and manual…
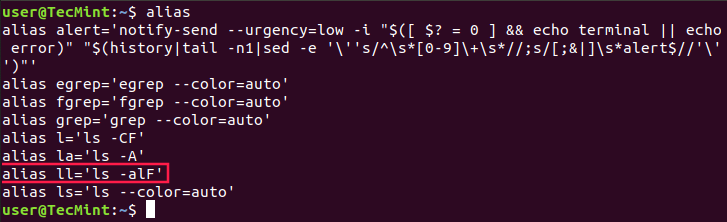
Linux users often need to use one command over and over again. Typing or copying the…

There are countless cloud storage platforms that provide safe and secure storage space for your files….
Because Falcon Identity Protection is part of the unified Falcon platform, Mondelēz didn’t have to integrate…
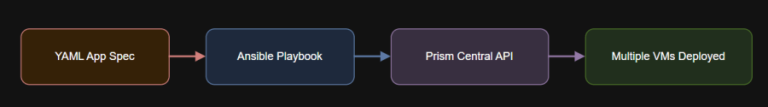
Introduction app_vms:- name: web01memory: 4096vcpus: 2disk: 20subnet: vlan10category: “env:prod”ansible-playbook deploy_app_stack.yml –ask-vault-pass -i inventory.yml Optional Enhancements Add…

File Transfer Protocol (FTP) was once a widely used method for transferring files or data remotely….