Legacy Apps and Azure Local SDN: Lifting and Shaping Networks Around Hard-Coded IPs
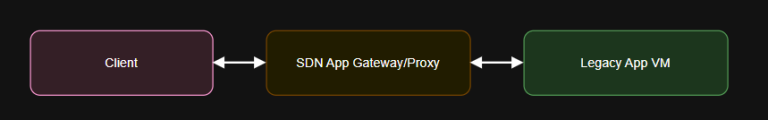
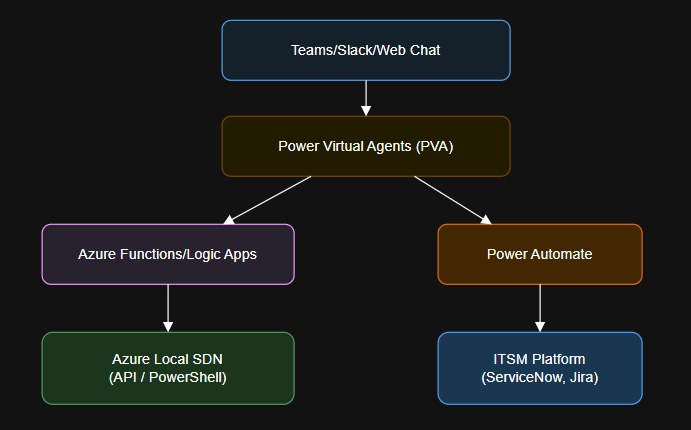
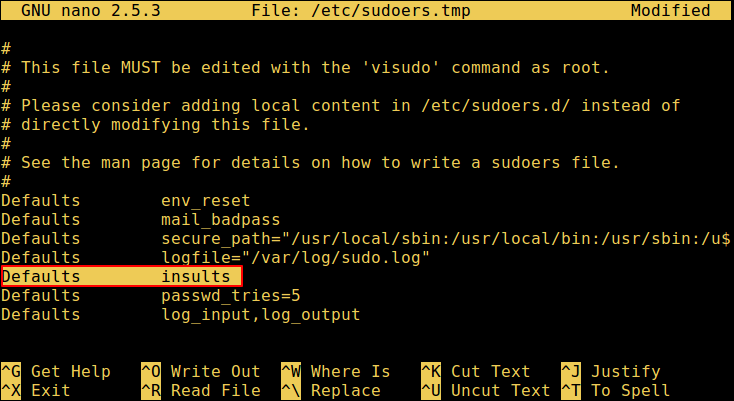
Introduction resource legacyDns ‘Microsoft.Network/privateDnsZones@2020-06-01’ = {name: ‘legacy.local’location: ‘global’}Diagram: Hard-coded static IPs Manual DNS or HOSTS file…