CrowdStrike 2026 Global Threat Report: The Evasive Adversary Wields AI
To defend themselves, security leaders need clarity on which adversaries to watch, the details of their…
To defend themselves, security leaders need clarity on which adversaries to watch, the details of their…
These content packs span multiple categories including application resilience, file discovery, Linux device control, and asset…
There are so many benefits of using a VPN (Virtual Private Network), some of which include…
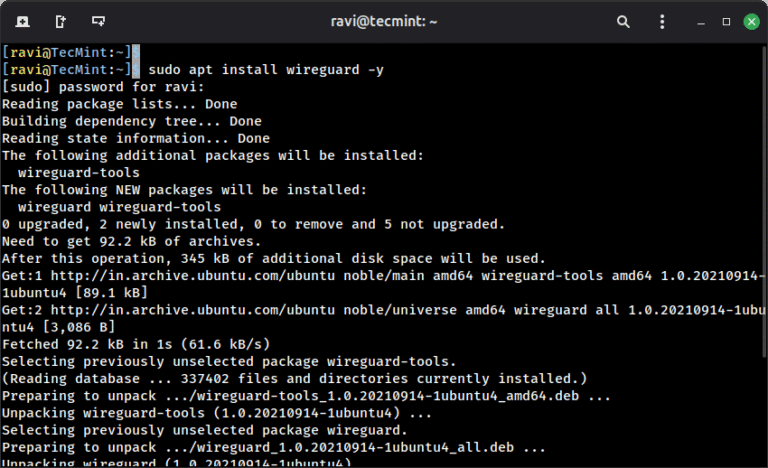
L2TP (which stands for Layer 2 Tunneling Protocol) is a tunneling protocol designed to support virtual…
Here, we examine a case study in which CrowdStrike OverWatch threat hunters identified and disrupted BLOCKADE…
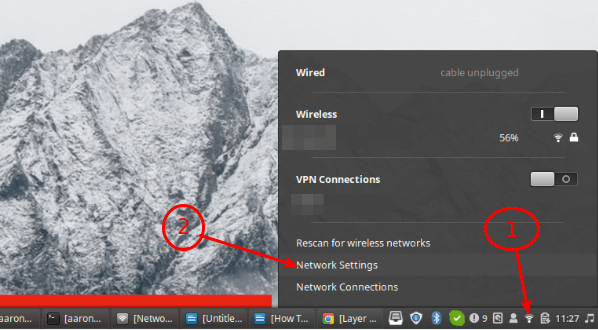
When you connect to a coffee shop’s WiFi or access the internet from any public network,…

There are countless cloud storage platforms that provide safe and secure storage space for your files….
Because Falcon Identity Protection is part of the unified Falcon platform, Mondelēz didn’t have to integrate…
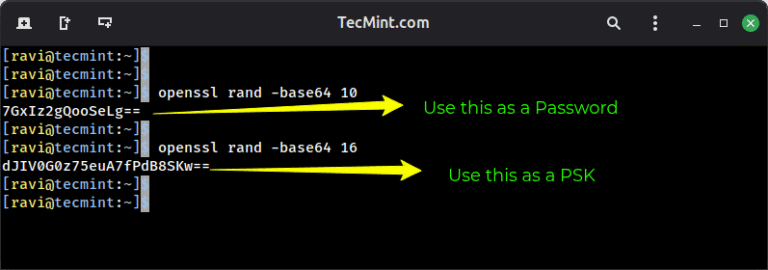
If you are a firm believer in browsing the internet securely, then you know how crucial…