Falcon for IT Supports Windows Secure Boot Certificate Lifecycle Management
A recommended execution cadence is weekly or monthly to maintain posture awareness and support audit requirements.While…
A recommended execution cadence is weekly or monthly to maintain posture awareness and support audit requirements.While…

By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…
This milestone underscores our commitment to protecting the federal government’s most critical systems from modern threats. …

Stopping compromised access at login is essential, but identity risk doesn’t end there. CrowdStrike acquired SGNL…
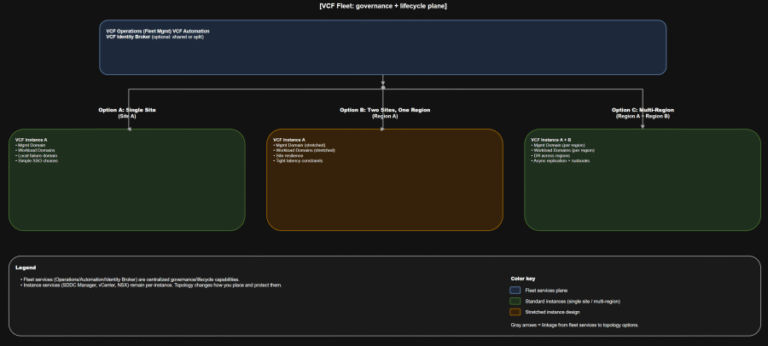
TL;DR Scope: VMware Cloud Foundation 9.0.0.0 GA (primary platform build 24703748) and the associated 9.0 GA…
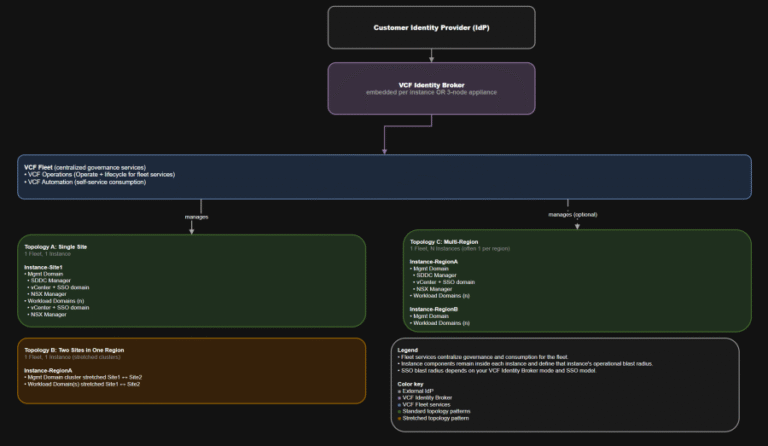
TL;DR Identity is not a “later” decision. It is a boundary decision. The hierarchy you should…
TL;DR This post targets VCF 9.0 GA only: VCF 9.0 (17 JUN 2025) build 24755599, with…
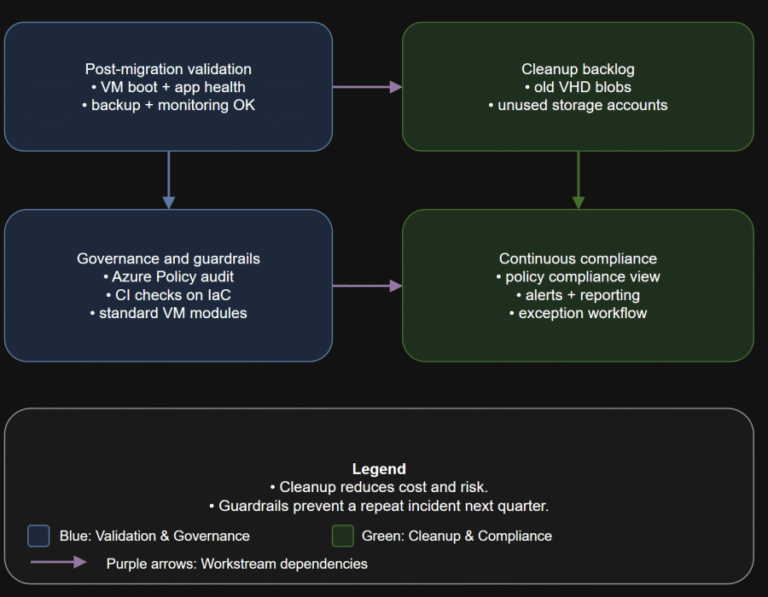
TL;DR Converting disks is not the finish line. Your real goal is a new steady state:…
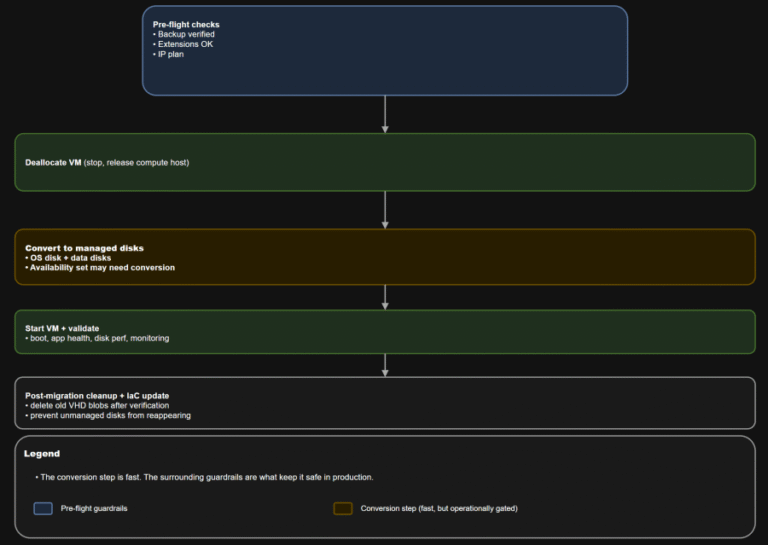
TL;DR Converting a VM to managed disks is usually operationally straightforward: deallocate, convert, start, validate. The…
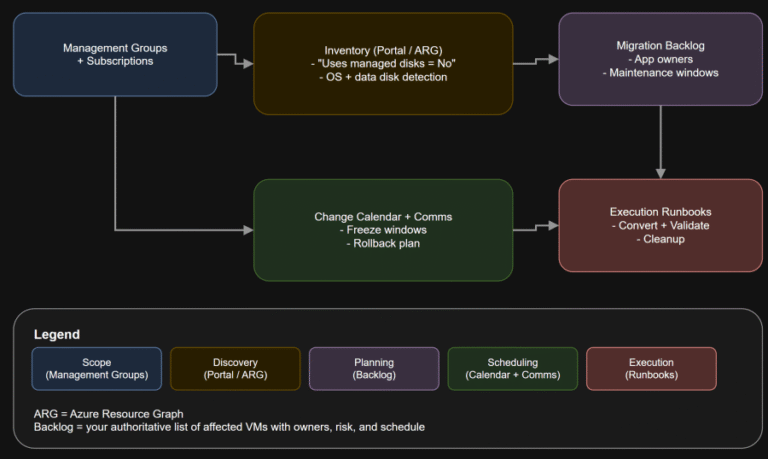
TL;DR If any Azure IaaS VM in your estate still uses unmanaged disks, it is on…
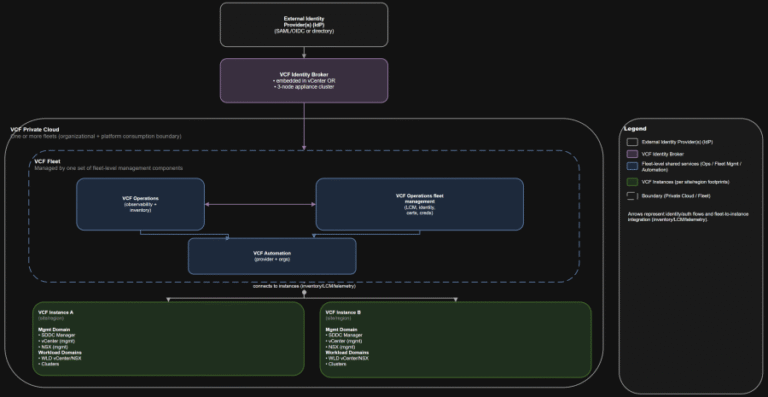
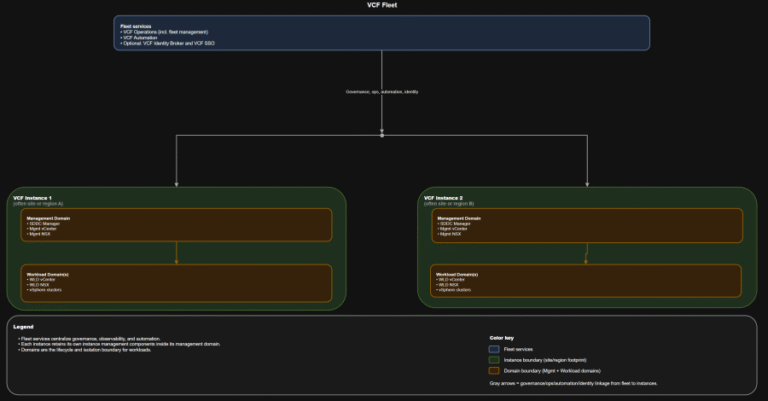
TL;DR Practical implication: if fleet services are impaired, governance and workflows degrade, but the instance-level control…
Indirect prompt injection significantly amplifies this risk by allowing adversaries to influence OpenClaw’s behavior through data…
As an example, consider a legitimate send_email tool that’s been thoroughly reviewed. An attacker publishes a…
– System Security Manager, Services (non-Government) IndustryThe truest assessment of the Falcon platform comes from the…
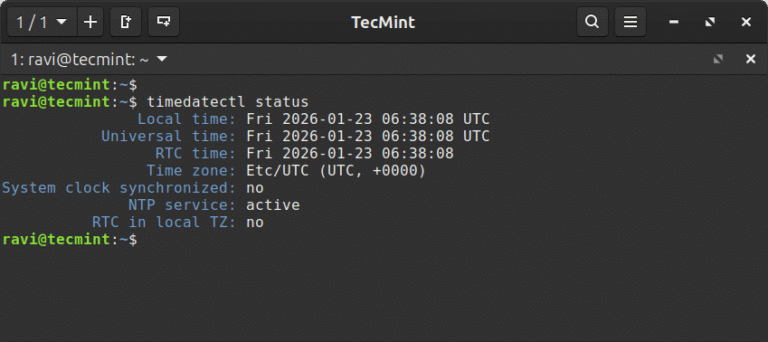
In this article, learn how to set time, timezone, and synchronize your Linux system clock with…