Detecting CVE-2026-20929: Kerberos Authentication Relay via CNAME Abuse
Before a client can authenticate to a service, it must resolve the service hostname to an…
Before a client can authenticate to a service, it must resolve the service hostname to an…
An initial spike on Linux platforms linked to runners was observed on March 19, 2026. The…
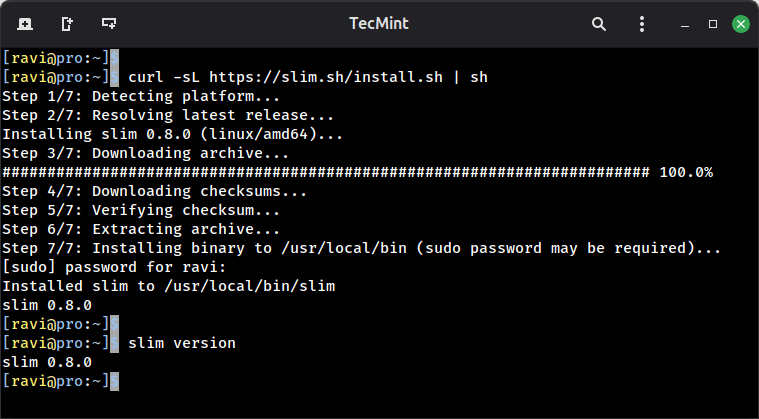
If you do any kind of local web development on Linux, you have almost certainly run…
SOCKS5 At launch, Enhanced Network Visibility will support parsing of plaintext HTTP requests and responses and…
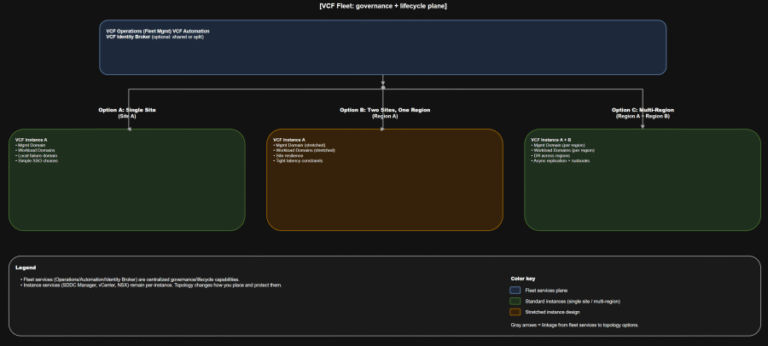
TL;DR Scope: VMware Cloud Foundation 9.0.0.0 GA (primary platform build 24703748) and the associated 9.0 GA…
As an example, consider a legitimate send_email tool that’s been thoroughly reviewed. An attacker publishes a…
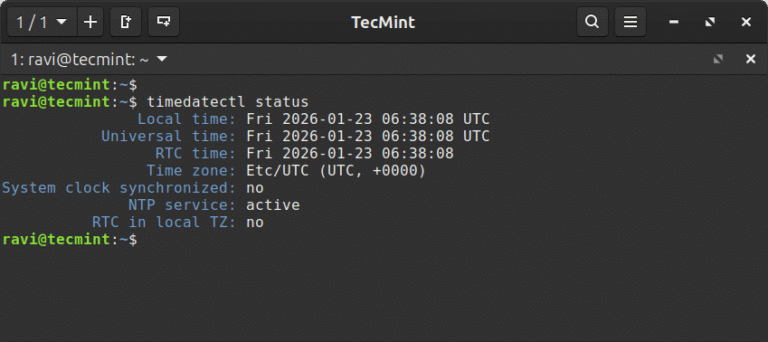
In this article, learn how to set time, timezone, and synchronize your Linux system clock with…
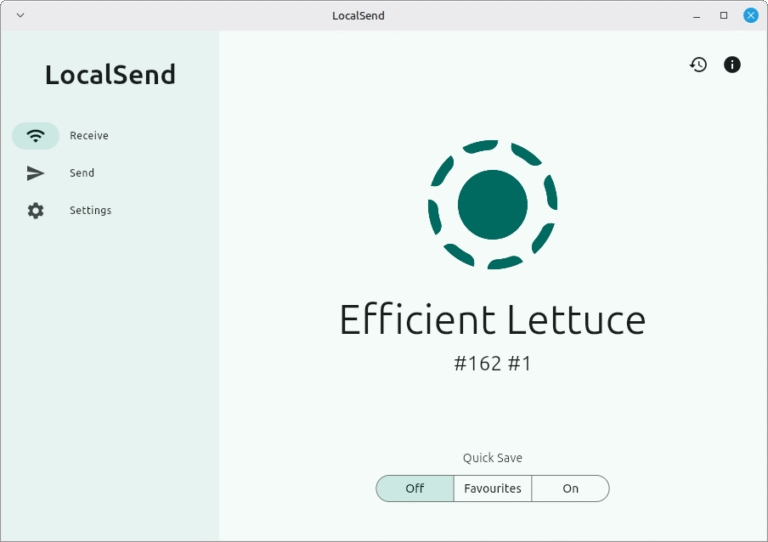
One of the most important uses of a network is for file sharing purposes, and there…
WARP PANDA demonstrates a high level of stealth and almost certainly focuses on maintaining persistent, long-term,…
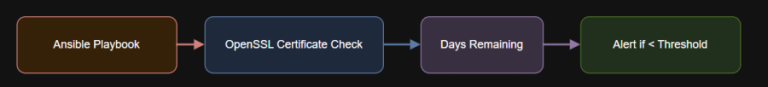
Introduction – name: Convert expiry date to epochset_fact:cert_expiry_date: “{{ cert_expiry_raw.stdout | trim }}”cert_expiry_epoch: “{{ cert_expiry_date |…