How to Use fsck to Check and Repair Linux Filesystem Errors
Linux filesystems are responsible for organizing how data is stored and retrieved. Over time – due…
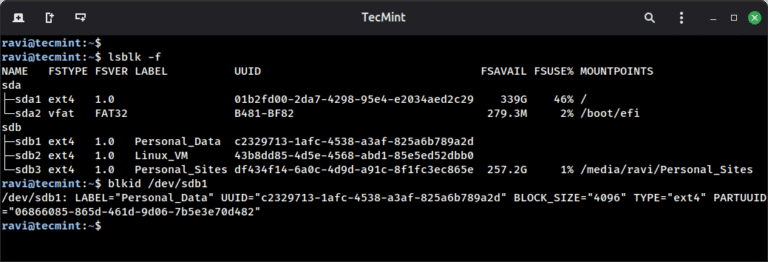
Linux filesystems are responsible for organizing how data is stored and retrieved. Over time – due…
Cloud environments are where AI is built, trained, and deployed at scale. Organizations are deploying AI…
This milestone underscores our commitment to protecting the federal government’s most critical systems from modern threats. …
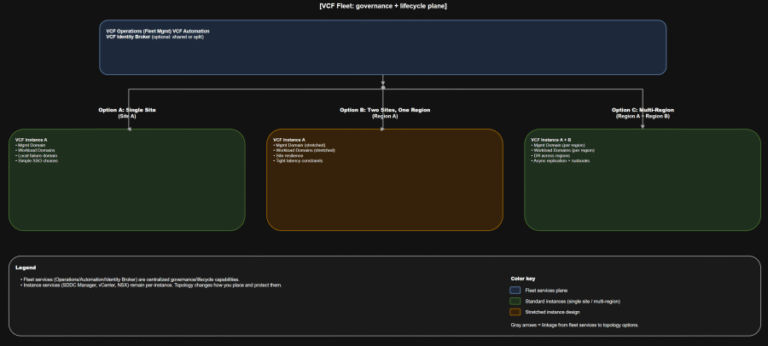
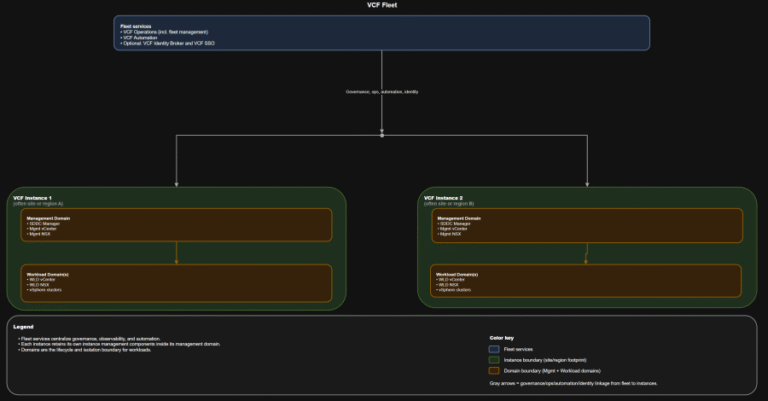
TL;DR Scope: VMware Cloud Foundation 9.0.0.0 GA (primary platform build 24703748) and the associated 9.0 GA…
TL;DR Identity is not a “later” decision. It is a boundary decision. The hierarchy you should…
CrowdStrike Falcon Identity Protection — A Great Tool to Gain Visibility We remain committed to innovating…
GOLDEN CHOLLIMA Shared infrastructure elements and tool cross-pollination indicate these units maintain close coordination. All three…
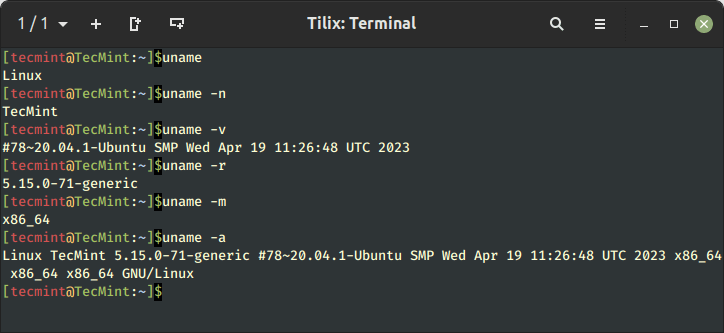
Learn 11 essential Linux commands to check hardware info including CPU, RAM, disk, USB, and PCI…
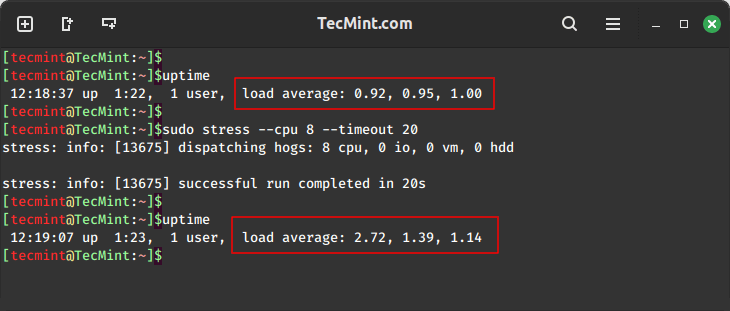
In this guide, we will explore two important tools, stress and stress-ng, for conducting comprehensive stress…
I’m delighted to announce CrowdStrike’s intent to acquire Seraphic, the leader in browser runtime security. With…
Pillar #1: A Rich Corpus of Human-refined Data In cybersecurity, AI agents don’t operate in a…
The AI era is here — and it’s redefining cybersecurity. Organizations around the globe are adopting…
When most people think about operating systems, they picture Windows laptops or MacBooks, but here’s what’s…
CrowdStrike uses NVIDIA Nemotron open models in CrowdStrike Falcon® Fusion SOAR and CrowdStrike Charlotte AI™ AgentWorks….
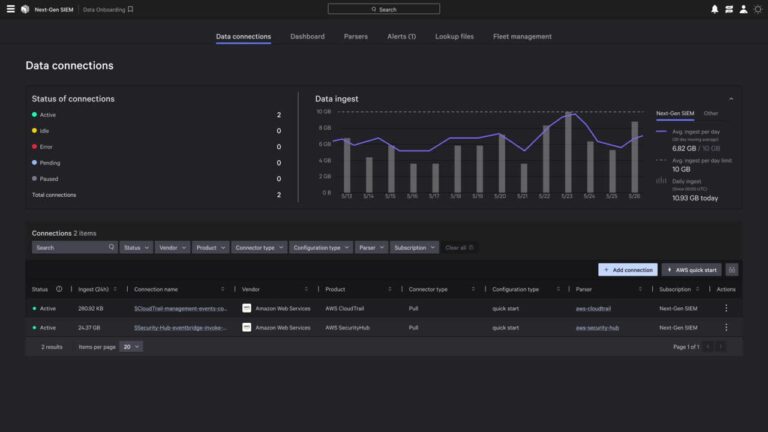
Perform on-demand queries for forensics, compliance, or audit use cases. CrowdStrike is the first cybersecurity partner…