From Scanner to Stealer: Inside the trivy-action Supply Chain Compromise
An initial spike on Linux platforms linked to runners was observed on March 19, 2026. The…
An initial spike on Linux platforms linked to runners was observed on March 19, 2026. The…
If you do any kind of local web development on Linux, you have almost certainly run…
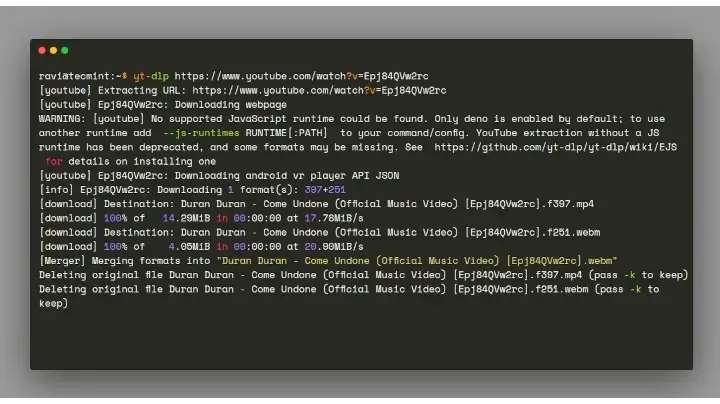
We all love listening to music and watching videos, whether it’s at the gym, at work,…
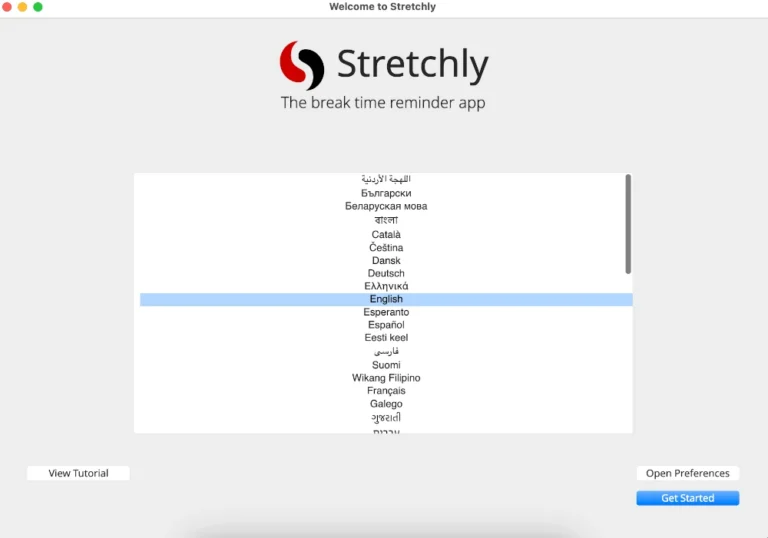
In this article, you will discover 3 excellent break reminder apps for Linux that help prevent…
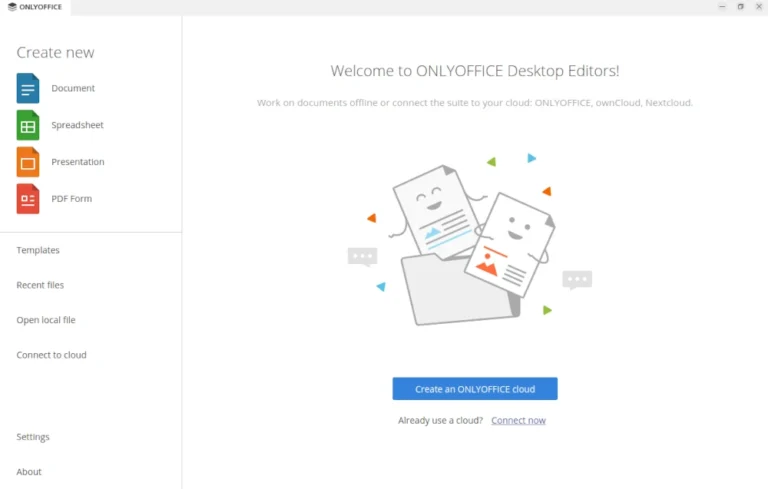
Updated: This article has been refreshed to cover the latest ways to edit documents on Ubuntu…
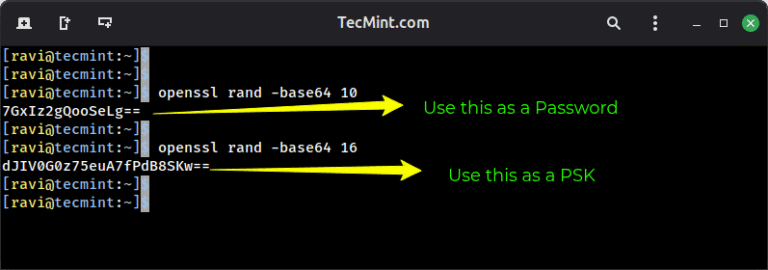
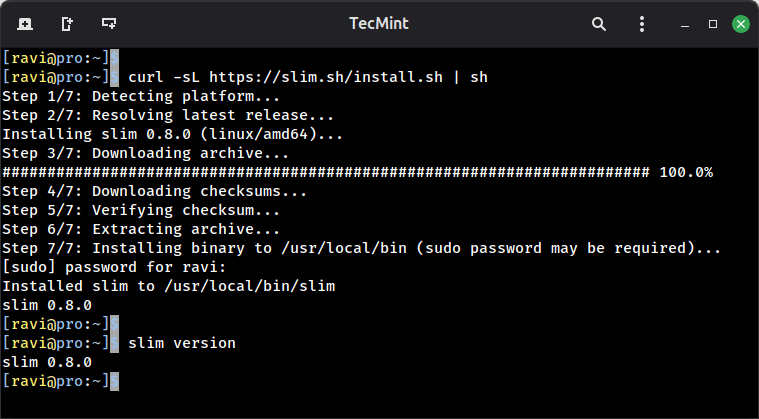
There are so many benefits of using a VPN (Virtual Private Network), some of which include…
Zero-Day Vulnerability in Windows Cloud Files Mini Filter Driver The CrowdStrike Falcon platform regularly collects and…
WARP PANDA demonstrates a high level of stealth and almost certainly focuses on maintaining persistent, long-term,…
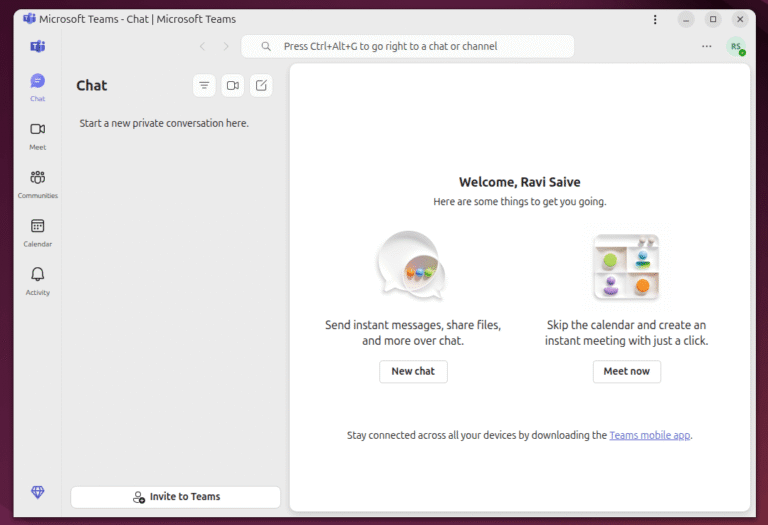
Gone are the days when Skype was the go-to VoIP tool for every chat, call, or…
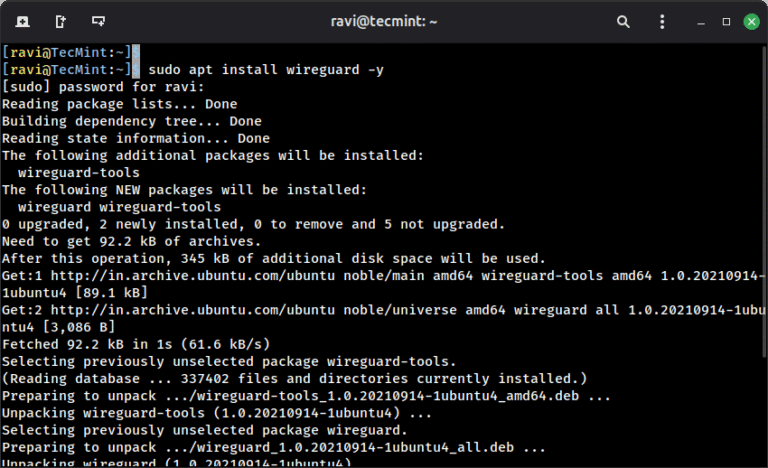
When you connect to a coffee shop’s WiFi or access the internet from any public network,…
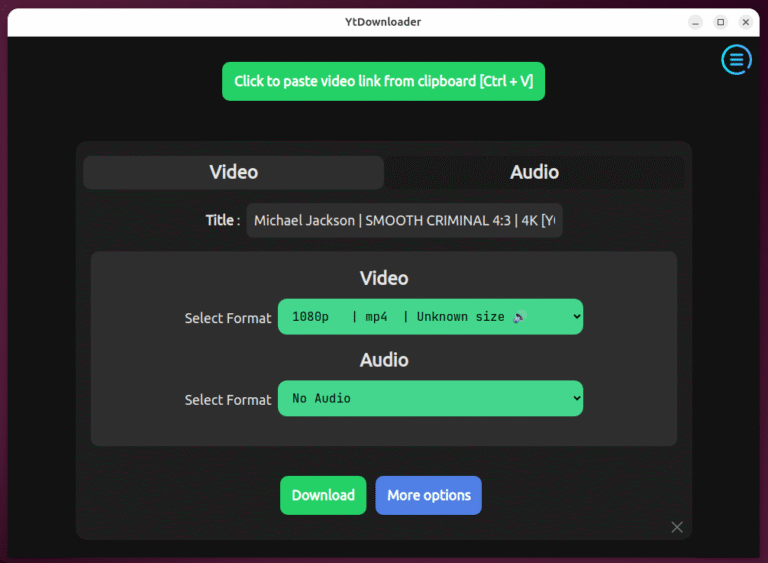
Earlier, I wrote about yt-dlp, the powerful command-line tool for downloading videos from hundreds of websites,…
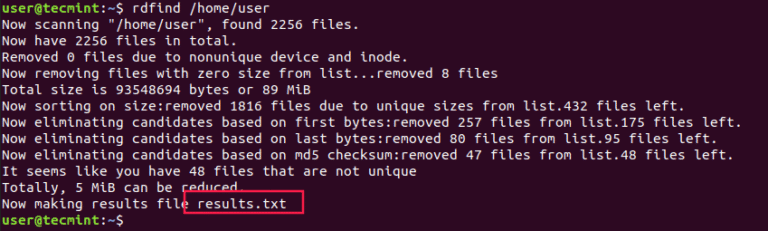
Organizing your home directory or even system can be particularly hard if you have the habit…
It isn’t easy to figure out which of the many Linux apps out there are actually…
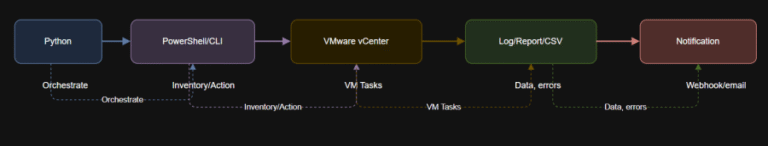
Learning Objectives VMware Repository on GitHub See how a single Python script can orchestrate inventory, lifecycle,…
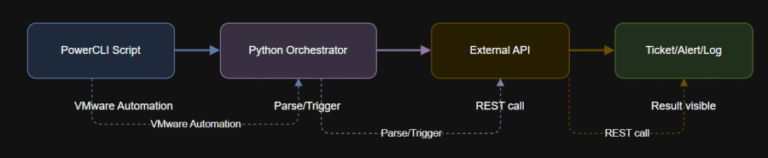
Learning Objectives $message = @{text = “VM $vmName has been powered off via automation.”} | ConvertTo-Json…