CrowdStrike Technical Risk Assessments Reveal Common Exposure Patterns
In our Technical Risk Assessments, we consistently find that this external footprint is larger and more…
In our Technical Risk Assessments, we consistently find that this external footprint is larger and more…
Innovation and Growth Recognized by Frost & Sullivan Our investment in AI security extends beyond automation…
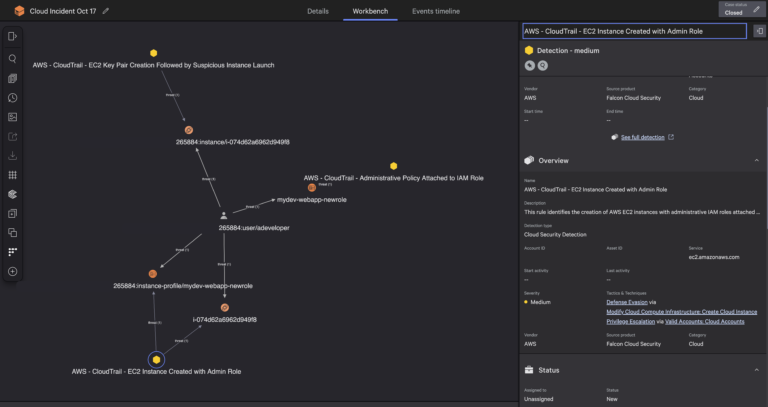
This shift is critical in today’s threat landscape. Adversaries move across identity, endpoint, and cloud in…

Complexity has become a defining security challenge as organizations expand across hybrid and multi-cloud environments. In…

By correlating runtime application behavior with cloud infrastructure findings, Application Explorer gives organizations a precise view…
Cloud environments are where AI is built, trained, and deployed at scale. Organizations are deploying AI…
As part of Falcon Cloud Security’s unified cloud-native application protection platform (CNAPP), Falcon ASPM helps organizations…
As AI adoption accelerated, WEX® — a global commerce platform that supports business operations primarily for…
With the cluster infrastructure in place through the Vertex Training Cluster, we configured Slurm, the industry-standard…

In the MUSTANG PANDA scenario, the adversary embedded encoded shellcode within their malware in an attempt…
Perform on-demand queries for forensics, compliance, or audit use cases. CrowdStrike is the first cybersecurity partner…
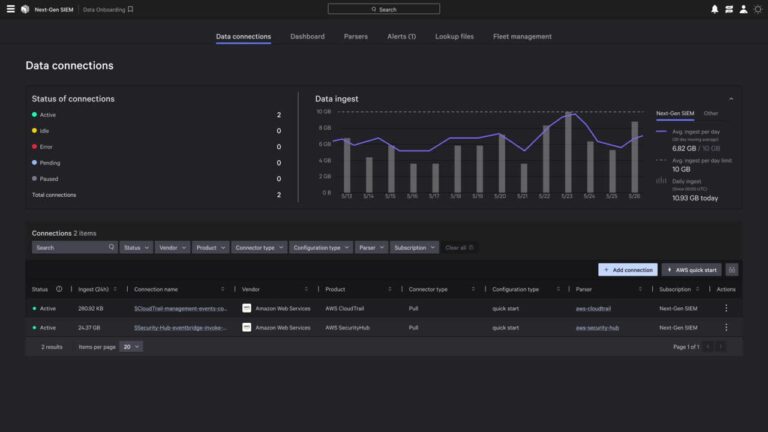
Falcon Cloud Security has implemented a new approach which processes cloud logs as they stream in…
Unified classification: Apply consistent classifications for financial data, personally identifiable information (PII), protection health information (PHI),…

These reports include:With Falcon Cloud Security data correlated in Falcon Next-Gen SIEM, teams can detect cross-domain…
This isn’t just about saving time. It’s about enabling every stakeholder to see, understand, and act…