How to Create HTTPS Local Domains for Your Projects
If you do any kind of local web development on Linux, you have almost certainly run…
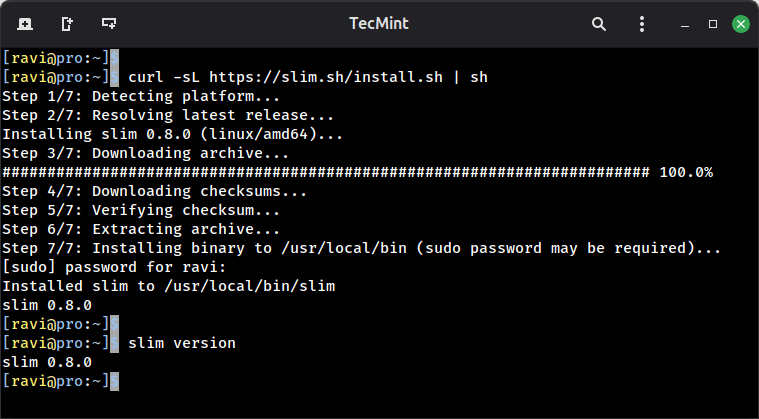
If you do any kind of local web development on Linux, you have almost certainly run…
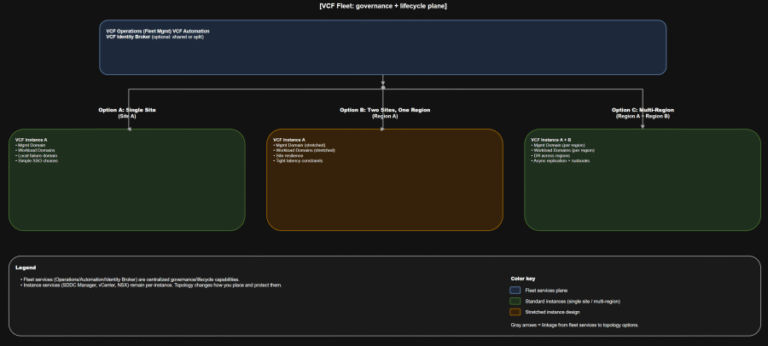
TL;DR Scope: VMware Cloud Foundation 9.0.0.0 GA (primary platform build 24703748) and the associated 9.0 GA…
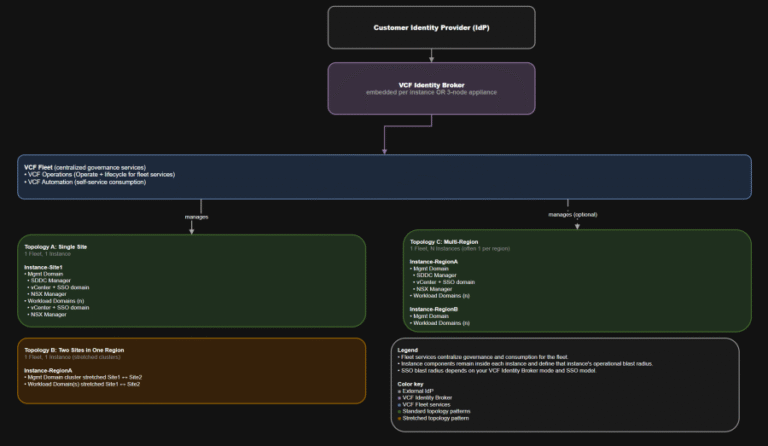
TL;DR Identity is not a “later” decision. It is a boundary decision. The hierarchy you should…
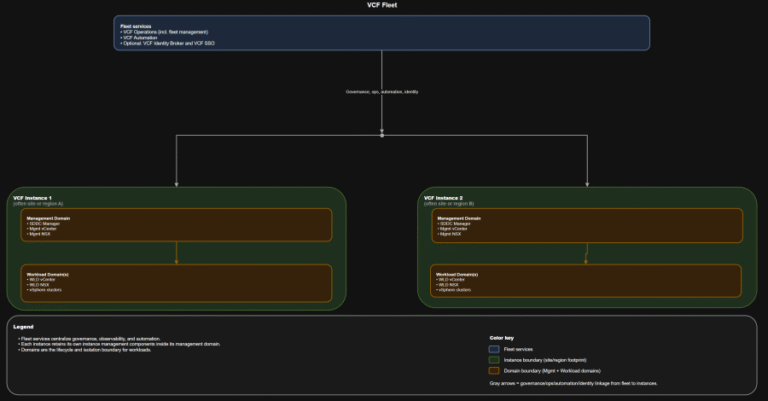
TL;DR This post targets VCF 9.0 GA only: VCF 9.0 (17 JUN 2025) build 24755599, with…
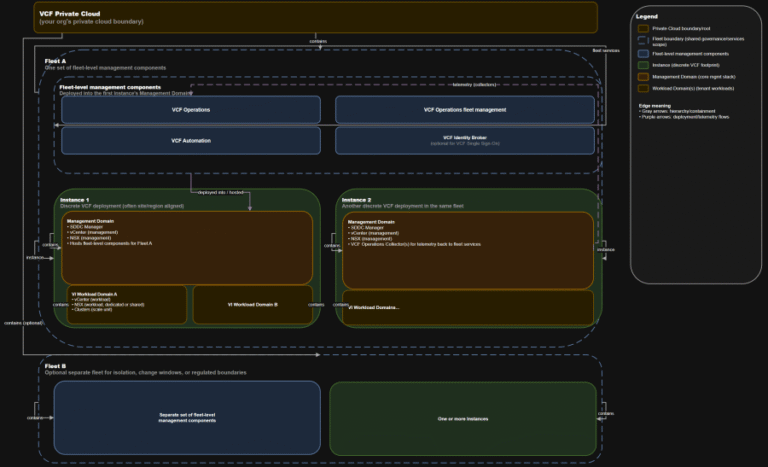
TL;DR A) One fleet, one instance, stretched where justified In VCF 9.0, identity is not a…
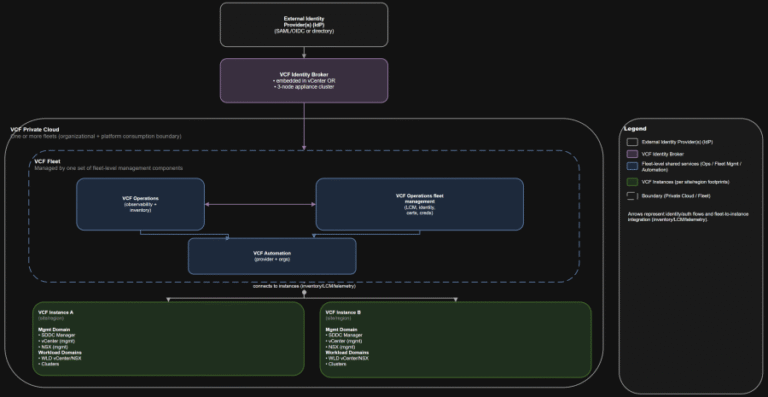
TL;DR Practical implication: if fleet services are impaired, governance and workflows degrade, but the instance-level control…
As an example, consider a legitimate send_email tool that’s been thoroughly reviewed. An attacker publishes a…
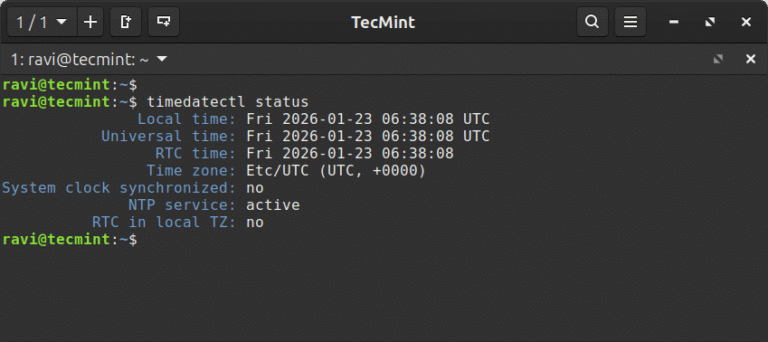
In this article, learn how to set time, timezone, and synchronize your Linux system clock with…
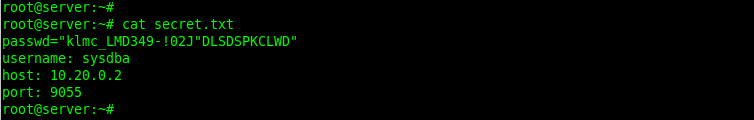
In this article, we show you how to encrypt files with GPG in Linux, generate key…
Actively Exploited Zero-Day Vulnerability in Windows Desktop Window Manager CVE-2026-20955 and CVE-2026-20957 are Critical remote code…
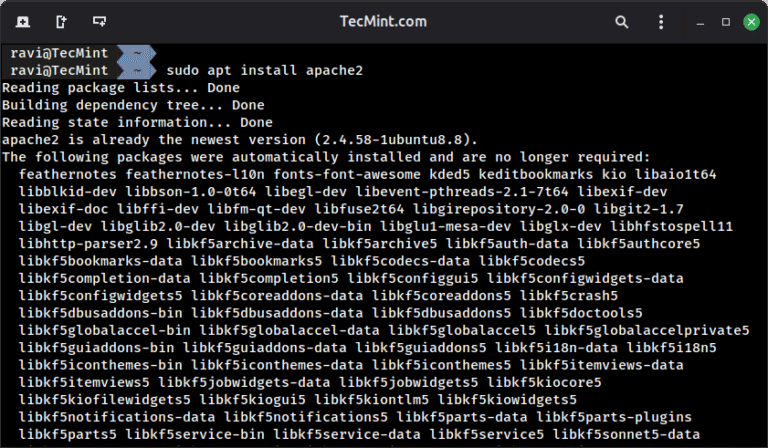
In this article, we will go through the various steps to install the constituent packages in…

When someone visits your website, their browser and your server exchange information back and forth. Without…
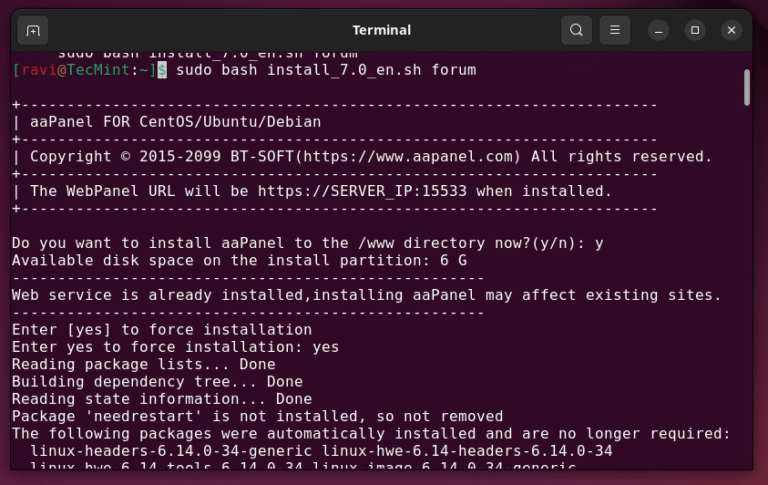
Managing a web server through command-line alone can feel like you’re juggling too many things at…
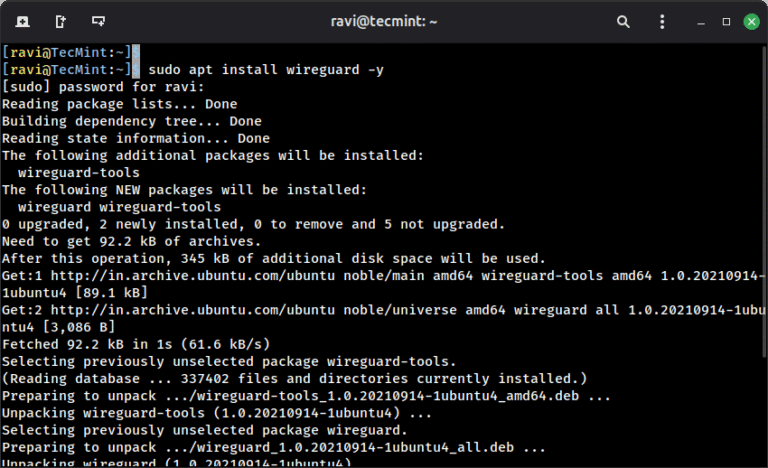
When you connect to a coffee shop’s WiFi or access the internet from any public network,…
Coerced Authentication The initial reconnaissance and setup phase requires minimal resources but careful planning. The attack…