7 layers of agentic AI – Governance Layer
Introduction if __name__ == “__main__”:# Example: Validate if a user action is allowed by enterprise policyinput_payload…
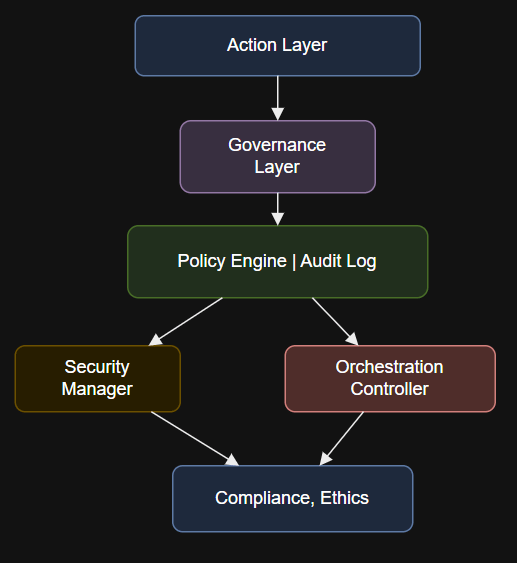
Introduction if __name__ == “__main__”:# Example: Validate if a user action is allowed by enterprise policyinput_payload…
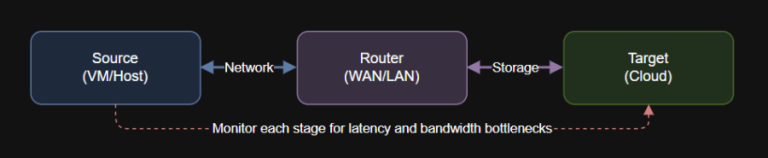
Introduction Data movement in cloud and hybrid architectures is only as fast as your slowest link….
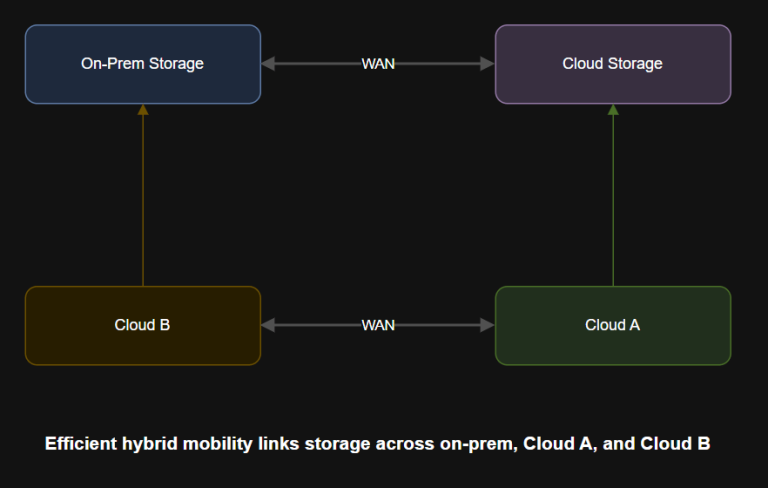
Introduction A media company needs to replicate video assets from on-prem storage to both Azure and…

Introduction A global retailer must store EU customer data within European borders to comply with GDPR….
The Adversary’s Path to Achieving Persistence Once SCATTERED SPIDER gains access to a target organization, they…
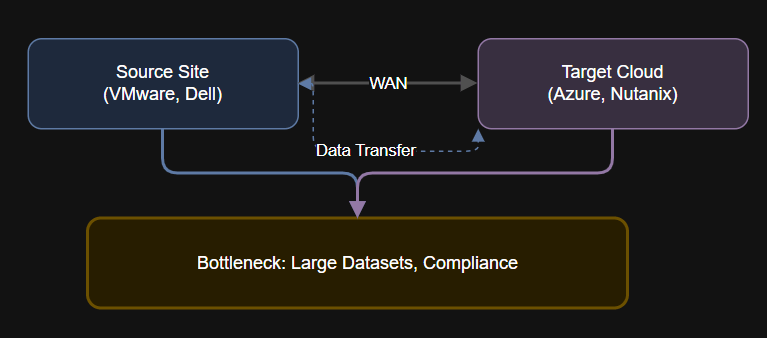
Introduction Even the best-planned cloud and hybrid migrations can be derailed by data gravity. When large…
Publicly Disclosed Zero-Day Vulnerability in Windows Kerberos As we have learned with other notable vulnerabilities, such…
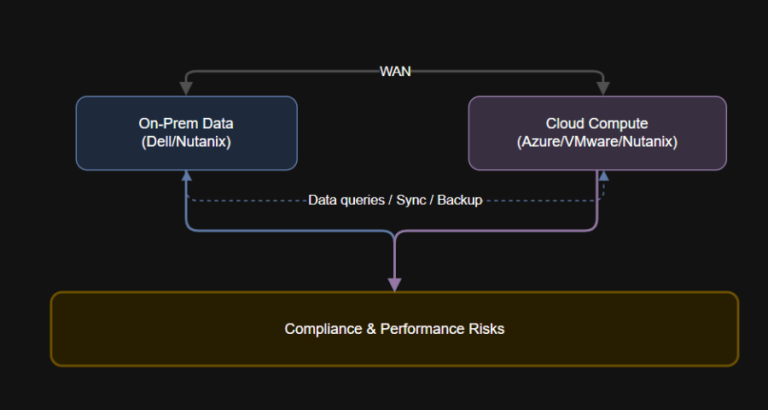
Introduction: What Is Data Gravity? Data gravity is a defining factor in successful cloud migration and…
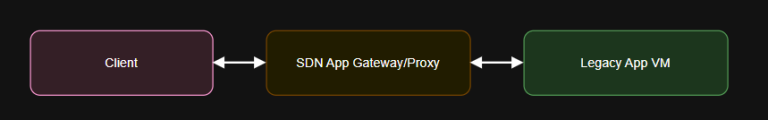
Introduction resource legacyDns ‘Microsoft.Network/privateDnsZones@2020-06-01’ = {name: ‘legacy.local’location: ‘global’}Diagram: Hard-coded static IPs Manual DNS or HOSTS file…
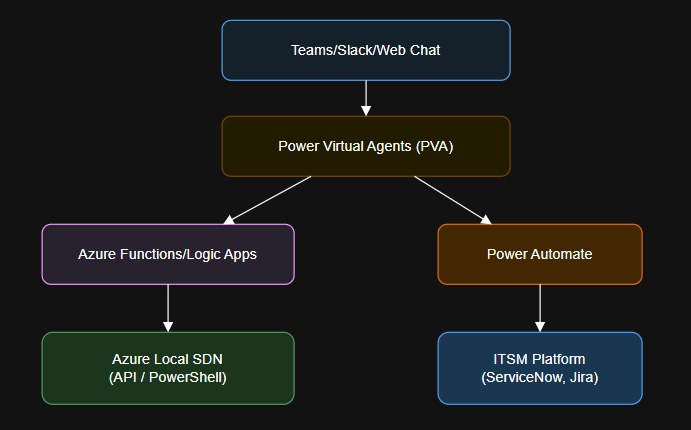
Table of Contents Introduction What Is ChatOps and Why Use It for Azure Local SDN? Architecture…
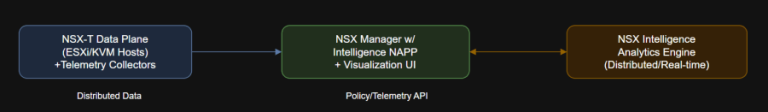
Table of Contents Introduction NSX Intelligence NAPP Architecture Deep Dive Real-World Deployment Patterns Microsegmentation with NSX…

Introduction Bicep Example: If you’re an architect or engineer aiming to master network automation, policy enforcement,…

Introduction Scenario:Manufacturing plant with strict separation between OT (operational tech) and IT, high security, and real-time…

Introduction Workflow 2: Telemedicine Visit Table of Contents Executive Overview Healthcare Security Challenges Solution Architecture Overview…
Publicly Disclosed Zero-Day Vulnerability in Microsoft SQL Server The CrowdStrike Falcon platform regularly collects and analyzes…